Cybersecurity is basically the protection of hardware, software and data that uses internet from cyberthreats. This is a practice done by individuals as well as enterprises to protect their data centers against unauthorized access. You must have heard about the incident where 300,000 computers in 150 countries malfunctioned due to worms (infecting virus) like WannaCry ransomware and lose around $4 billion, think about how is it possible for emerging companies to survive in such ambushing environment? Yes, we need someone to stop such attacks. And most importantly, that next life-saving person can be you. This blog brings you a complete guide on how to build a successful career in Cyber Security.
This Blog Includes:
Check Out: Career in Cyber Law
What is Cyber Security?
Simply put, Cyber Security provides us a set of preventive tools and techniques that are used to protect precious data from being breached. The fundamental role of Cyber Security is to build an expert who can act as a preventive wall to deal with major threats like:
- Cyber Terrorism: Information technology is exploited by terrorist groups to attain information for their own self-purpose. Attackers usually attack infrastructure, telecommunications, networks, and computer systems.
- Cyber Warfare: In such warfare, nations use information technology to scrape the data out of foreign country networks. It is considered as the 5th domain of warfare following up the land, sea, air, and space.
- Cyber Espionage: It involves the practice of controlling information technology to get into someone’s confidential data without prior permission of the owner. It is mostly utilized to gain economic, military, and political leverage by using various virus injecting activities.
Prerequisites for a Cyber Security Career
There is a lack of skilled cybersecurity professionals who can deal with daily cybersecurity challenges. Therefore, several companies are looking for people who have cybersecurity skills. For example, companies like Google, and Microsoft. However, to get work in the cybersecurity field it is important to meet the cybersecurity requirements. These are listed below:
- The applicant must have a Bachelor’s degree in a technical field.
- Those who don’t possess a background in cybersecurity can take advantage of cybersecurity courses available
- Other skills such as networking and knowledge of operating systems is essential
Cybersecurity Skills
Some of the essential skills to gain employment in the cybersecurity domain are as follows. These skills have to be learnt by a person to excel in the cybersecurity field.
- Have an understanding of firewalls, web proxy, VPN, and IDS/IPS
- Be proficient with coding languages such as Python, Java, HTML, and PHP
- Must have excellent information regarding networking, encryption techniques, and routing protocols
- Must be aware of the best practices to identify and access management (IAM)
- Additionally, knowledge of SQL and Database Management systems is essential. The applicant must also possess problem-solving skills.
Career in Cyber Security in 2023
Even though there are so many career paths in Cyber security but the presence of fun associated with each path will make you think twice. Especially, when you are a tech lover. Here are the top Cyber Security careers in 2023:
- Security Architect
- Ethical Hackers
- Information Security Analyst
- Computer Forensics Analysts
- Chief Information Security Officer
- IT Security Consultant
- Penetration Tester
- Security System Administrator
- Security Software Developer
- Security Consultant
Security Architect
What if we tell you that this is suitable for you if you care about solving problems and strategising? Cool, isn’t it? If you go this path, you will be hired to construct and execute network and computer security for an organization. It’s all about generating complex security framework and ensuring whether the function malfunctions or not. Being security Architect, you have to counter DDoS attacks and various kind of hacking.
Ethical Hackers
These hackers hold a certificate in their hand called CEH (Certified Ethical Hacker) and receive a license by their employers before invading the security of systems. The magic behind hiring an Ethical Hacker for defense is to know about the vulnerabilities. Such hackers use the same malicious exploitive techniques that hackers use to gain unauthorized access. So as an ethical hacker in cyber security, you only need to show the vulnerabilities. Explore more about Ethical Hacking Courses!
Read: Here’s How You can Become a Ethical Hacker
Information Security Analyst
This type of analyst defense in the front gate of networks. They arrange firewalls and do encryption to prevent breaches. Along with this, they steadily monitor the network to watch out abnormal activities.
Computer Forensics Analysts
The work of a forensic analyst is to keep a check on cyber crime. Such analysts work with law enforcement powers in the private and public sectors organizations. They are assigned a range of tasks that includes following up data trails, analyzing records, interpretation of data linked to crime, and recovering deleted files. Such forensic analysts must keep a well profound record with themselves so that they can later provide evidence in the court against the guilty ones.
Chief Information Security Officer
It’s a mid-executive level position in which the work of the chief is to manage the operations of a company or an organization. They strike a right balance to coordinate, plan and direct all the data security needs, networks, and computers of the employer. CISCO merge themselves with the management so that they can estimate the company’s required cyber security demands. At last, it’s necessary for you to have a strong background in IT security strategy, architecture, communication, and human resources skills to become a CISCO.
Know all about CCIE-CISCO Certification here!
IT Security Consultant
They meet with clients to give them advice on how they can stay on the safe side. These kind of consultants are more likely to be hired by small agencies that don’t have a budget to handle their security matters. Still, these consultants are also hired by big corporations.
Read more about Building a Successful Career in Information Security!
Penetration Tester
Such testers look out for system flaws. They perform a series of hacking activities to get into a network and computer systems to discover the latent vulnerabilities of the operating system, application problems, improper configurations, and service in advance. A penetration tester should be highly skilled who can keep highly precise records of their observed vulnerabilities and activities.
More Info: Penetration Testing Certification Courses
Security System Administrator
The responsibility of a security system administrator is relatable to various cyber security jobs. For example, they are required to administer, install, troubleshoot, and maintain computers, data networks, and distinctive security systems. The only line that separates the security system administrator and other cyber security professionals are the positions. An administrator is a chief who controls the daily operations of security systems. You need to monitor, run regular backups, set up, delete, and maintain individual user accounts to be a security system administrator. On the other side, they are also meant to develop organizational security procedures.
Security Software Developer
The name itself suggests that what security software developer do. You simply need to develop and integrate protecting software during the design and development of the application software. Whether you build it alone or with a team, it depends on the company and your specific position.
Security Consultant
This is an all in one expert. Such experts consult numerous organizations on the basis of their experience and knowledge. They measure cyber security risks and give precise treatment. But one thing is for sure, as a security consultant, you have to puzzle yourself in a wide range of variables while evaluating security systems because of the diverse industries and companies.
Salary
Here is the average salary of top Cybersecurity careers and jobs in India in 2021:
| Career in Cybersecuirty | Salary |
| Network Security Engineer | 4-8 Lakhs per annum |
| Cybersecurity Manager | 12 Lakhs per annum as the starting salary |
| Cyber Security Analyst | 6 Lakhs per annum as the starting salary |
| Chief Information Security Officer (CISO) | 2 Crores to 4 Crores per annum |
| Security Architect | 17 Lakhs per annum as the starting salary |
Explore the Difference Between Information Security and Cyber Security!
Cyber Security Courses
To set up a career in the field of a choice it is necessary to have the right educational qualifications. Here are the top Cyber Security courses:
Also read: Cyber Security Courses after 12th
- Bachelor of Networking and Cyber Security
- Bachelor of Information Technology (Network Security)
- Bachelor of Cyber Security
- Bachelor of Science in Cyber Security and Forensics
- BSc in Cyber Security
- Bachelor of Computer Science Cyber Security
- Bachelor of Information Technology Network and Cyber Security System
- Bachelor of Science in Computer Security
- BSc Hons Computer Forensics
- Bachelor of Computer Science in Digital System Security
Also read: Master’s Level Cyber Security Courses
- Master of Science in Ethical Hacking and Cyber Security
- Master of CyberSecurity
- PG Diploma in Cyber Security
- MEng in Cyber Security Engineering
- Master of Engineering Management
- Master of Networking Cyber Security
- MSc Cyber Security Masters
- Master of Information Security and Digital Forensics
- Postgraduate Diploma in IT Security Management
Also read: Cyber Security Online Courses
Top Universities for Cyber Security
- Georgia Institute Of Technology
- Massachusetts Institute of Technology
- University of California, Berkeley
- University of Southern California
- New York University (NYU)
- The University of Maryland, College Park
- University of Washington
- Johns Hopkins University (J.Hopkins)
- Iowa State University
- Melbourne Institute of Technology
- TAFE NSW Institutes
- Deakin University
- Murdoch University
- Edith Cowan University
- Coventry University
- Swinburne University of Technology
- De Montfort University
- University of Southampton
- University of Surrey
- University of London
Career Scope
Having a career in cyber security can be “Next Big Achievement” for you. Now you must be wondering what is so special about having the next big achievement? We can achieve big in any other field too. Right? Of course, it is great to have a stable career in any field but cyber security is one of the booming modern careers because of the constant growth of hackers.
Here are the pros of a career in Cyber Security:
- Startups and Rapid Technological Transformations: Many new startups are taking participation in the international economy day by day such as Zomato, Swiggy, Policybazaar, Paytm, etc. In addition to this, bots are developed by companies to make their work easier so that they can stand apart from the crowd. So not a single business owner can afford to lose the data of their customers.
- Deficiency of Cyber Security Experts: Last year, ESG(Enterprise Strategy Group) did its annual global survey on the state of IT. It claimed that in 2018, 51 respondents claimed that their organizations were in a terrible shortage of cybersecurity skills.
- Good Pay Package: According to the Bureau of Labor Statistics, cybersecurity professionals earn from $20.76 to $57.67 per hour.
- Can Work From Anywhere Around The World: When hackers can smash into high-security networks from anywhere then why can’t you be the hero and save the victim from anywhere? If you are that kind of person who doesn’t like to stay in one place for a long time then this career will be suitable for you.
- Innovative and Creative Field: Do you hate to play by the rules? If yes, then as a cybersecurity expert you have full control over your steering. That means, nobody can deny your methods. You can throttle or break your shuttle as per your needs. It will be your game and your rules because to do something innovative, you have to break rules. So employers won’t shuffle with your methods because you can breach security in your own way.
- Self-Study: Unlike Engineering, medicines or humanities, you can learn it on your own and get certification to become a Cyber security professional.
8 Strategic Tips to Start a Career in Cybersecurity
Data protection is crucial to every industry. For this reason, the demand for cybersecurity professionals is high. Companies prefer cyber security professionals for security, sustainability, and growth. Below we have listed 8 strategic tips that can be used to start a career in security.
- Gain knowledge about cybersecurity by investing in Cybersecurity education
- Stay on top of Industry trends. That is, keep up with the industry publications, events, and certifications
- Gain cybersecurity certification from credible sources
- Gain industry experience and network with other cybersecurity professionals
- Build soft and hard skills related to cybersecurity
- Specialize in a niche and become an industry expert
- Create a portfolio that highlights the experience attained by the individual
- Finally, search for job openings and apply online
FAQs
To set up a career in Cyber Security, you must first secure a bachelor’s degree. At the UG level, you can choose from the aforementioned bachelor’s courses in the particular field. But if you already have a bachelor’s degree in some other related field you can go for a masters degree in CyberSecurity, following which you can secure a job in this industry.
The amount you earn being a Cyber Security agent or analyst varies from country to country. In India, Cyber Security agents earn around INR 8,00,000 to INR 9,00,000.
There are a few online courses through which you can learn on your own. But if you aspire to set up a career in a field like CyberSecurity, where practical knowledge plays a crucial role, you must strive to learn the insights of the field through experts and via getting enrolled into full-time courses.
To pursue a career in Cyber Security as well as excel in the field, it is necessary for one to have a sound knowledge of mathematics.
When it comes to career paths, there are a lot of choices for you. However, we recommend you to pursue the path which suits with your passion. So, if a career in Cyber Security is something that excites you, but you are not sure how to go about it, just call a study abroad expert at Leverage Edu right now
-
Best article I have ever read on Career in Cyber Security.
Thanks
-
Thanks, Sharath. Send it to your friends who want to make a career in cybersecurity.
-
Sure
-
-
-
Greatly written article. Thank You!!!!
-
Hi Rohit, thanks for your wonderful feedback! To know more about Cyber Security, read our blog on https://leverageedu.com/blog/diploma-in-cyber-security/.
-

 One app for all your study abroad needs
One app for all your study abroad needs













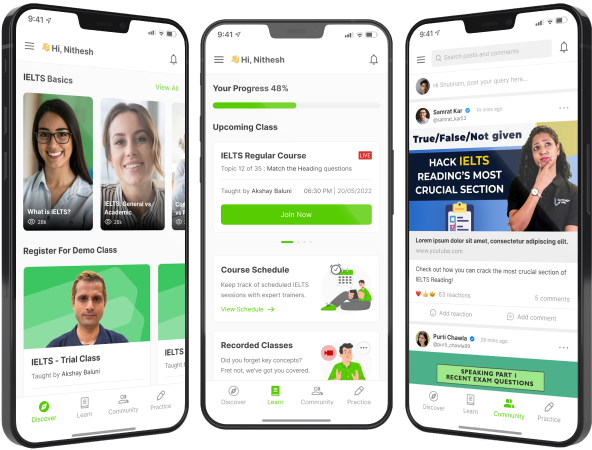





 45,000+ students realised their study abroad dream with us. Take the first step today.
45,000+ students realised their study abroad dream with us. Take the first step today.


9 comments
Best article I have ever read on Career in Cyber Security.
Thanks
Thanks, Sharath. Send it to your friends who want to make a career in cybersecurity.
Sure
Greatly written article. Thank You!!!!
Hi Rohit, thanks for your wonderful feedback! To know more about Cyber Security, read our blog on https://leverageedu.com/blog/diploma-in-cyber-security/.
Can you make an article on some of the best courses in pen testing?
Your content is awesome!!
Hi Utkarsh, thanks for your suggestion! We would definitely try to put up a blog on Pen Testing courses. Subscribe to our newsletter to stay updated with the latest courses and careers!
Can i take this course after complete 10th std
Hi Emam, get in touch with our experts at 88262 00293 to if you can take up this course after completing class 10th. You can also register here for a free career counselling session – https://leverageedu.com/admissions/study-abroad-admission/.